UPX Free VPN Private Browser Fast Secure Web Proxy for PC: UPX Free VPN Private Browser Fast Secure Web Proxy is a free Tools App which has a rating of 4.6 out of 5.0 till now. The App was developed by the Unblock Vpn Proxy Browser and at the moment it has
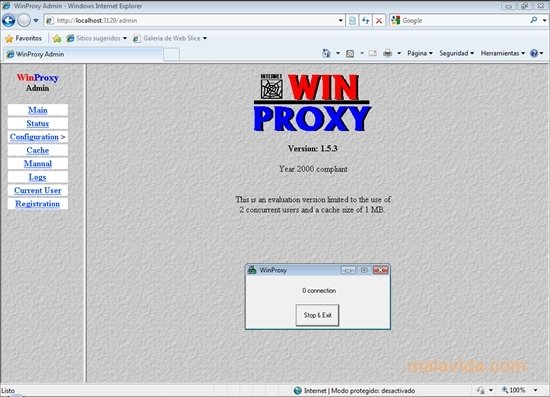
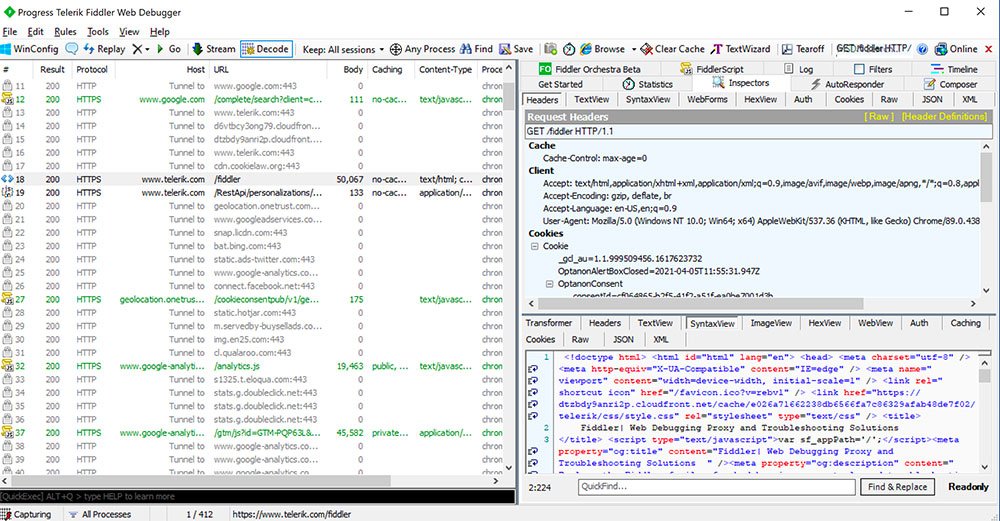
To have your Mac detect whether a proxy is necessary and automatically configure the proxy settings, enable the “Auto Proxy Discover” checkbox. Your Mac will use the Web Proxy Auto Discover protocol, or WPAD, to automatically detect whether a proxy is necessary. This setting may be used on business or school networks, for example. Platform: Windows, Mac, Android, iOS. Sleipnir is a free web browser that lets you quickly locate the specific tab even when you have over 100 tabs open. It works on the Blink engine and supports Chrome function extensibility (for Windows OS). Fiddler Everywhere is a secure and modern web debugging proxy for macOS, Windows, and Linux. Fiddler Everywhere is a powerful tool to modify the response before it reaches the browser to test and debug web applications. Fiddler Everywhere integrates with. Wireshark is one of the most widely used, if not the most widely used, network. Unblock Youtube with SudoProxy free SSL web proxy. Use SudoProxy to unblock restricted websites in any country. Surf website anonymously hiding IP address and online identity with SudoProxy Free SSL web proxy.
 1,000,000+ Installs on Android devices and many more on PC using Emulators. UPX Free VPN Private Browser Fast Secure Web Proxy has the latest version of v87.0.4280.141 which was updated last on February 11, 2021. Its a fun App for everyone and the least required android version to run the App is 5.0 and up.
1,000,000+ Installs on Android devices and many more on PC using Emulators. UPX Free VPN Private Browser Fast Secure Web Proxy has the latest version of v87.0.4280.141 which was updated last on February 11, 2021. Its a fun App for everyone and the least required android version to run the App is 5.0 and up.Contents
- 1 How to Download UPX Free VPN Private Browser Fast Secure Web Proxy for PC (Windows 10, 8, 7 & Mac OS X)
UPX Free VPN Private Browser Fast Secure Web Proxy Developer’s Description
We are going to use Android emulator to install UPX Free VPN Private Browser Fast Secure Web Proxy on your laptop. These android emulators simulate the android environment in your laptop and allow you to install and use apps available on google play store. Bluestacks and MEmu play are the two top most emulators available on the internet. So let’s see how we can use these emulators to install your favourite app – UPX Free VPN Private Browser Fast Secure Web Proxy on your PC. UPX Free VPN Private Browser Fast Secure Web Proxy is regarded as one of the best apps in Tools category. With a simple and interactive UI, the App has got a huge popularity among the android users. So without further ado lets look at the App details. If you have not yet downloaded the UPX Free VPN Private Browser Fast Secure Web Proxy on android you can head to Playstore. We have provided the link below this paragraph. And if you want to use it on PC you can follow the rest of the guide.
UPX Free VPN Private Browser Fast Secure Web Proxy App Details
| App Name | UPX Free VPN Private Browser Fast Secure Web Proxy |
| Category | Tools |
| Developed by | Unblock Vpn Proxy Browser |
| Installs | 1,000,000+ |
| Current Version | 87.0.4280.141 |
| Require Android | 5.0 and up |
| Last Updated | February 11, 2021 |
| Rating | 4.6/ 5 |
| Total no of Ratings | 59,524 |
Also Read: Spell amp Play: Vehicles PC (Mac OS – Windows 10, 8, 7).
Download UPX Free VPN Private Browser Fast Secure Web Proxy for Android
In addition, the App UPX Free VPN Private Browser Fast Secure Web Proxy is very interactive and fun to use and the users can enjoy it at any time and anywhere around the world. What are you waiting for? download now UPX Free VPN Private Browser Fast Secure Web Proxy on your smart devices from link below. Enjoy the App UPX Free VPN Private Browser Fast Secure Web Proxy and go as far as you can. Have fun!
Download: UPX Free VPN Private Browser Fast Secure Web Proxy (Google Play Store)
Recommended: Ares Virus for PC ( Windows/Mac) – Free Download.
How to Download UPX Free VPN Private Browser Fast Secure Web Proxy for PC (Windows 10, 8, 7 & Mac OS X)
To download and install UPX Free VPN Private Browser Fast Secure Web Proxy on PC we will be needing Android Emulator or an Android OS as the App developers have released it on Android platforms only. By using Android emulator we can easily use any App or play any game for Android on our PC or laptop computers. Below we have provided the link of an article which will guide you how can you download an Android Emulator of your choice and install it on your PC.
How to install UPX Free VPN Private Browser Fast Secure Web Proxy for PC and Laptop
Now it’s our turn to download and install UPX Free VPN Private Browser Fast Secure Web Proxy on PC using the emulator we have downloaded and installed. All we need to do for that is simply open the Emulator we installed and configure it using our Google Email, as we normally do in Android Devices. when we are done with the Gmail configuration on Play Store simply Open the Play Store and Search ‘UPX Free VPN Private Browser Fast Secure Web Proxy’ and Select the App to install. Then click on the Install button to start the installation or Pay the price to get the installation started if the App is Paid. Once installed, Click ‘open’ to run UPX Free VPN Private Browser Fast Secure Web Proxy for PC. That’s All.
Follow Geeky Tips for more guides like this and let us know if you liked the guide above.
If you have any queries regarding the tutorial or the usage of App leave your feedback in the comment section below.
By continuing to use the site, you agree to the use of cookies. more information
The cookie settings on this website are set to 'allow cookies' to give you the best browsing experience possible. If you continue to use this website without changing your cookie settings or you click 'Accept' below then you are consenting to this.
How to remove 'Proxy Virus' from Mac?
What is 'Proxy Virus'?
Proxy Virus (also known as MITM Proxy Virus) is a type of browser-hijacking program that has recently become popular. In order to spread this infection, cyber criminals often use various adware-type applications. In most cases, these infiltrate computers without users' permission. Adware is also likely to deliver intrusive advertisements and record information relating to browsing activity.
The initial adware installation process seems normal. After installation, however, users are presented with a deceptive pop-up message encouraging them to update the Safari web browser. After clicking 'OK', users are presented with another pop-up that asks users to enter account credentials. In this way, users might inadvertently grant adware permission to control the Safari browser. Additionally, rogue installers deploy a 'bash script' designed to connect to a remote server and download a .zip archive. The archive is then extracted and a .plist file contained within it is copied to the LaunchDaemons directory. The .plist file contains a reference to another file called 'Titanium.Web.Proxy.Examples.Basic.Standard'. Two additional scripts ('change_proxy.sh' and 'trush_cert.sh') are executed after the next reboot. The 'change_proxy.sh' script is designed to change the system proxy settings, thereby making it use HTTP/S proxy at 'localhost:8003'. The 'trush_cert.sh' script is designed to install a trusted SSL certificate into the keychain. Cyber criminals responsible for this infection use Titanium Web Proxy - an open-source asynchronous HTTP(S) proxy writen in C Sharp (C#). Titanium Web Proxy it is a cross-platform proxy, meaning that it can run on various operating systems, including MacOS. The purpose of this infection is to hijack search engines. Cyber criminals use it to modify Internet search results. Using a proxy to achieve this is rather unusual, since cyber criminals typically employ fake search engines. They use various browser-hijacking applications to modify settings (e.g., new tab URL, default search engine, homepage) by assigning them to certain URLs. Promoted websites often seem normal and their design is usually similar to Bing, Yahoo, Google, and other legitimate search engines. Yet, fake search engines can generate results that lead to malicious websites. Moreover, noticing that such browser settings have been modified is simple because users continually encounter redirects to dubious sites. Using tools such as Proxy Virus is more difficult for these criminals, and yet also more reliable from their point of view. Cyber criminals also deliver fake search results by modifying the content of legitimate search engines. For instance, if a user attempts to search using the Google search engine, the entire website (URL, header, footer, etc.) is genuine, however, the infection modifies the result section. In this way, users are fed with fake results even though they search using legitimate engines. Ultimately, this behavior can lead to further high risk infections - users might inadvertently visit malicious websites. Additionally, cyber criminals use such tactics to increase the traffic of certain websites, which allows them to generate revenue through advertising. The presence of Proxy Virus significantly diminishes the browsing experience and can lead to further computer infections. As mentioned above, adware-type applications are designed to deliver advertisements (e.g., coupons, banners, pop-ups, etc.). These ads might also redirect to malicious websites and even run scripts designed to download/install other unwanted apps. Therefore, clicking them can also lead to installation of infectious apps. Additionally, ads are delivered using tools that enable placement of third party graphical content on any site. Therefore, they often conceal website content, thereby diminishing the browsing experience. Adware-type apps gather information such as IP addresses, website URLs visited, pages viewed, search queries, and other similar details, which are later shared with third parties (potentially, cyber criminals). These people generate revenue by misusing private data. Therefore, information tracking might eventually lead to serious privacy issues, or even identity theft. You are advised to remove all infections, including adware and Proxy Virus.
| Name | MITM Proxy virus |
| Threat Type | Mac malware, Mac virus, Proxy hijacker, Search hijacker |
| Detection Names (Adobe Flash Player-3.dmg - Fake Adobe Flash Player installer) | Avast (MacOS:Agent-EN [Drp]), BitDefender (Adware.MAC.Bundlore.DMM), Emsisoft (Adware.MAC.Bundlore.DMM (B)), Kaspersky (Not-a-virus:HEUR:AdWare.OSX.Bnodlero.q), Full List (VirusTotal) |
| Symptoms | You see inaccurate search results, your Mac and Internet speed become slower than normal, you see unwanted pop-up ads, you are redirected to dubious websites. |
| Distribution methods | Deceptive pop-up ads, free software installers (bundling), fake flash player installers, torrent file downloads. |
| Damage | Internet browsing tracking (potential privacy issues), display of unwanted ads, redirects to dubious websites, loss of private information. |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
There are dozens of adware-type applications and browser hijackers online. Typically, these applications offer 'useful features' in attempts to give the impression of legitimacy and trick users to install, however, the only purpose of these applications is to generate revenue for the developers. Rather than giving any real value for regular users, PUAs cause redirects, deliver advertisements, modify settings, and record information.
How did potentially unwanted applications install on my computer?
Adware and browser-hijacking applications are usually proliferated via intrusive advertisements and a deceptive marketing method called 'bundling' - stealth installation of third party applications together with regular (usually free) software. Developers know that users often rush download/installation processes and skip steps. Therefore, 'bundled' apps are usually concealed behind 'Custom/Advanced' settings (or other sections) of these procedures. By carelessly skipping download/installation steps and clicking on advertisements, many users expose their systems to risk of infections and compromise their privacy.
How to avoid installation of potentially unwanted applications?
To prevent this situation, be very cautious when browsing the internet and downloading/installing software. We strongly recommend that you download your software from official sources only, preferably using direct download links. Third party downloaders/installers are typically monetized using the 'bundling' method, and thus such tools should never be used. Do some research before downloading unknown software just to confirm that it is legitimate and virus-free. Intrusive advertisements typically seem legitimate, however, once clicked, they redirect to dubious websites (gambling, adult dating, pornography, and similar). If you continually encounter these ads and redirects, remove all suspicious applications and browser plug-ins immediately. If your computer is already infected with PUAs, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate them.
Fake Adobe Flash Player installer promoting Proxy Virus (step 1):
Fake Adobe Flash Player installer promoting Proxy Virus (step 2):
Instant automatic Mac malware removal:Manual threat removal might be a lengthy and complicated process that requires advanced computer skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for MacBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited seven days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- STEP 1. Remove PUA related files and folders from OSX.
- STEP 2. Remove rogue extensions from Safari.
- STEP 3. Remove rogue add-ons from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.

Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your 'Applications' folder:
Click the Finder icon. In the Finder window, select 'Applications'. In the applications folder, look for 'MPlayerX','NicePlayer', or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited seven days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Remove mitm proxy virus related files and folders:
Click the Finder icon, from the menu bar. Choose Go, and click Go to Folder...
Check for adware-generated files in the /Library/LaunchAgents folder:
In the Go to Folder... bar, type: /Library/LaunchAgents
In the “LaunchAgents” folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - “installmac.AppRemoval.plist”, “myppes.download.plist”, “mykotlerino.ltvbit.plist”, “kuklorest.update.plist”, etc. Adware commonly installs several files with the same string.
Check for adware generated files in the /Library/Application Support folder:
In the Go to Folder... bar, type: /Library/Application Support
In the “Application Support” folder, look for any recently-added suspicious folders. For example, “MplayerX” or “NicePlayer”, and move these folders to the Trash.
Check for adware-generated files in the ~/Library/LaunchAgents folder:
In the Go to Folder bar, type: ~/Library/LaunchAgents
In the “LaunchAgents” folder, look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware - “installmac.AppRemoval.plist”, “myppes.download.plist”, “mykotlerino.ltvbit.plist”, “kuklorest.update.plist”, etc. Adware commonly installs several files with the same string.
Check for adware-generated files in the /Library/LaunchDaemons folder:
In the Go to Folder... bar, type: /Library/LaunchDaemons
In the “LaunchDaemons” folder, look for recently-added suspicious files. For example “com.aoudad.net-preferences.plist”, “com.myppes.net-preferences.plist”, 'com.kuklorest.net-preferences.plist”, “com.avickUpd.plist”, etc., and move them to the Trash.
Scan your Mac with Combo Cleaner:
If you have followed all the steps in the correct order you Mac should be clean of infections. To be sure your system is not infected run a scan with Combo Cleaner Antivirus. Download it HERE. After downloading the file double click combocleaner.dmg installer, in the opened window drag and drop Combo Cleaner icon on top of the Applications icon. Now open your launchpad and click on the Combo Cleaner icon. Wait until Combo Cleaner updates it's virus definition database and click 'Start Combo Scan' button.
Combo Cleaner will scan your Mac for malware infections. If the antivirus scan displays 'no threats found' - this means that you can continue with the removal guide, otherwise it's recommended to remove any found infections before continuing.
After removing files and folders generated by the adware, continue to remove rogue extensions from your Internet browsers.
MITM Proxy virus removal from Internet browsers:
Remove malicious extensions from Safari:
Remove mitm proxy virus related Safari extensions:
Open Safari browser, from the menu bar, select 'Safari' and click 'Preferences...'.
In the preferences window, select 'Extensions' and look for any recently-installed suspicious extensions. When located, click the 'Uninstall' button next to it/them. Note that you can safely uninstall all extensions from your Safari browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Safari.
Remove malicious plug-ins from Mozilla Firefox:
Remove mitm proxy virus related Mozilla Firefox add-ons:
Open your Mozilla Firefox browser. At the top right corner of the screen, click the 'Open Menu' (three horizontal lines) button. From the opened menu, choose 'Add-ons'.
Choose the 'Extensions' tab and look for any recently-installed suspicious add-ons. When located, click the 'Remove' button next to it/them. Note that you can safely uninstall all extensions from your Mozilla Firefox browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Mozilla Firefox.
Remove malicious extensions from Google Chrome:
Free Web Proxy For Mac Computer
Remove mitm proxy virus related Google Chrome add-ons:
Vpn Proxy For Mac
Open Google Chrome and click the 'Chrome menu' (three horizontal lines) button located in the top-right corner of the browser window. From the drop-down menu, choose 'More Tools' and select 'Extensions'.
In the 'Extensions' window, look for any recently-installed suspicious add-ons. When located, click the 'Trash' button next to it/them. Note that you can safely uninstall all extensions from your Google Chrome browser - none are crucial for normal browser operation.
- If you continue to have problems with browser redirects and unwanted advertisements - Reset Google Chrome.
Would this malware give the 'bad guys' access to victims' SSL traffic? Could passwords and VPN credentials be captured by this route?